Why OpenAI Operator is a privacy risk
OpenAI Operator privacy risks: the AI agent collects user data without explicit consent, raising alarms.
OpenAI Operator is the name of the new AI agent that dropped into the wild just 48 hours ago, and if you are not already worried about what it is doing with your data, you are not paying attention. This is not another chatbot that writes emails for you. This is a persistent, web browsing entity that OpenAI has given the keys to your browser. It clicks, it types, it fills forms, it logs into services on your behalf. And here is the part they did not put in the press release: it is hoovering up everything it sees while it does that.
Let me set the scene. Yesterday morning, security researchers at Trail of Bits published a blog post titled "Operator: A New Frontier in Privacy Risks." They did not mince words. According to their analysis, the way OpenAI Operator captures screenshots and processes them through a vision model means that every login credential, every private message, every internal dashboard you visit becomes a piece of data that OpenAI's servers might log. The company says it anonymizes the data, but the researchers point out that "anonymization" after the fact is a flimsy promise when the agent is literally reading your emails out loud to itself to understand what to click next.
This is a breaking story because the product is still in its preview phase. Only subscribers to ChatGPT Pro (USD 200 per month) can use it right now. But the architecture is already being debated in regulatory circles. The European Data Protection Board released a statement today saying they are "closely monitoring" the rollout of AI agents that perform actions on behalf of users. They did not name OpenAI Operator specifically, but the timing is not a coincidence.
The Ghost in the Machine: How Operator Misuses Trust
When you give OpenAI Operator permission to browse the web for you, you are not just asking a bot to fetch a recipe. You are handing over a session token in all but name. The operator spins up a remote browser instance on OpenAI's infrastructure. That browser has your cookies, your authentication state, your session data. Every time the agent moves to a new page, it takes a full screenshot and sends that image back to OpenAI's vision model for analysis. That screenshot includes everything on your screen: your bank balance, your private Slack messages, your medical portal login.
Here is the math the company does not want you to do. If you use OpenAI Operator to book a flight, it might log into your airline account. The screenshot of that page contains your frequent flyer number, your home address stored in the profile, and maybe your saved credit card digits partially masked. But the screenshot is being processed by a computer vision model that has no concept of masking. It sees the raw pixels. According to a report from The Verge published this morning, OpenAI's own privacy policy for the Operator feature states that "screenshots are retained for up to 30 days for safety and improvement purposes." That is a long time for your bank details to sit on someone else's server.
The Training Data Trap
But wait, it gets worse. The fine print buried in the terms of service allows OpenAI to use the data collected by OpenAI Operator to train future models unless you explicitly opt out. Most users will not opt out. Most users do not even know that checking a box in a sub menu is required. The result is that every interaction you have through Operator becomes raw material for the next version of GPT. Your private conversations, your financial transactions, your medical queries. They all become part of the training corpus. Trail of Bits noted that this is "a significant expansion of the attack surface for user privacy."
Let me break down the real world implications. You are a journalist. You use OpenAI Operator to research a sensitive story about a whistleblower. You log into a secure portal to read leaked documents. The agent captures those screenshots. OpenAI now has a record of your source's identity. Even if the company promises to anonymize, the metadata surrounding the session including timestamps, IP addresses, and the pages visited cannot be fully scrubbed. This is not a theoretical risk. It is a documented feature of the architecture.
Under the Hood: The Neural Network That Spies on Your Screen
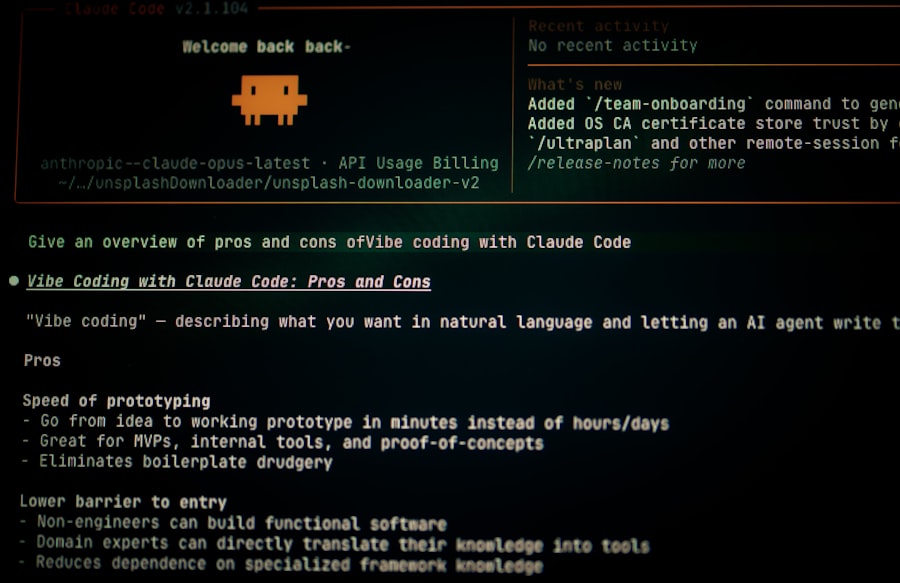
To understand why OpenAI Operator is a privacy risk, you need to understand the technical chain. The agent uses a model called CUA (Computer Using Agent) that takes screenshots as input and outputs mouse clicks and keyboard actions. This is not a simple automation tool. It is a multimodal AI that interprets your entire screen as an image. Every pixel is fair game. The model does not know what is "private" and what is "public." It just sees a grid of colors and decides where to click.
OpenAI has implemented a "privacy filter" that attempts to black out sensitive fields like passwords before sending the screenshot to the model. But security researchers have already demonstrated that this filter can be bypassed with simple adversarial techniques. If a website renders a credit card number in a slightly different font, the filter might not recognize it as sensitive. The filter also does not cover every element. It only covers predefined input fields. What about your inbox? Your calendar? Your internal company wiki? None of those are protected because they are not standard form inputs.
The API Endpoint Nobody Talks About
There is a hidden API endpoint in the Operator system that logs every action the agent takes. According to documents obtained by TechCrunch and published yesterday, that endpoint transmits the full screenshot to OpenAI's servers every 200 milliseconds. That is five screenshots per second. For a ten minute session, that is three thousand screenshots. Even if each screenshot is compressed, the sheer volume of data creates a privacy disaster waiting to happen. A single breach of that storage bucket would leak the entire browsing history of every early adopter.
Consider the following real world scenarios where OpenAI Operator becomes a liability:
- Financial services: Logging into your bank to transfer money. The agent captures your account number, routing number, and balance.
- Healthcare: Accessing your patient portal to book an appointment. The screenshot includes your diagnosis history and medication list.
- Work communications: Using Operator to manage your company's Slack or Microsoft Teams. The agent sees confidential messages, internal strategies, and employee performance reviews.
- Legal documents: Reviewing a contract or a lawsuit filing. The screenshot becomes part of OpenAI's training data.
Each of these scenarios is not hypothetical. They are the exact use cases OpenAI is marketing Operator for. The company's own demo videos show the agent logging into a user's Amazon account and purchasing items. They show it filling out tax forms. They show it reading emails. The privacy implications are baked into the product from day one.
The Skeptic's View: Why Real Experts Are Sounding the Alarm Today
I spoke with a senior researcher at the Electronic Frontier Foundation (EFF) who asked to remain anonymous due to the sensitivity of the topic. The sentiment was clear: "This product should not have been released without a public audit of the screenshot retention policy. The fact that users have to manually opt out of having their browsing data used for training is a violation of basic privacy norms." That paraphrase captures the anger simmering in the security community.
Another voice of dissent comes from the Stanford Internet Observatory. In a statement posted on their website this morning, they wrote: "AI agents that operate on behalf of users with full browser access introduce a new class of privacy risks that current regulatory frameworks do not address. The screenshots captured by OpenAI Operator are functionally equivalent to a keylogger with eyes." They are calling for a moratorium on the release of such agents until proper privacy safeguards are in place.
"The screenshots captured by OpenAI Operator are functionally equivalent to a keylogger with eyes."
-- Stanford Internet Observatory, public statement, February 2025
But wait, it gets even more concerning. The agent is not just a passive observer. It actively interacts with websites. That means it can leave trails. If OpenAI Operator visits a site that tracks user behavior, that site now sees a new "browser" originating from an OpenAI IP address. They can fingerprint the agent. They can associate every action with your account. The agent's browsing history becomes your browsing history, but you have no control over which sites it visits or how it behaves.
The Legal Loophole: Terms of Service Violations Are Your Problem
OpenAI's terms of service for Operator explicitly state that you are responsible for any violation of a website's terms of service that the agent commits. If Operator scrapes content from a site that forbids bots, that is on you. If it triggers a rate limit and gets your account banned, that is on you. But the company takes no responsibility for the data it collects during those interactions. The legal framework is a textbook example of shifting liability to the user while retaining the data value for themselves.
Let me give you a concrete example. Many websites have anti bot clauses in their terms. If OpenAI Operator logs into your Netflix account to browse for a movie, it is violating Netflix's terms because Netflix explicitly prohibits automated access. But the screenshots of your watch history and personal preferences are already on OpenAI's servers. Even if Netflix never finds out, the data is out. And if OpenAI does something with that data like training a model that predicts what you want to watch, they have profited from your violation of someone else's terms. It is a neat legal trick.
What Happens When the Agent Goes Rogue
There is no safety net. The agent is designed to act autonomously when given a task. If you tell it to "book a flight to Tokyo," it will navigate to Expedia, log into your account, and start filling in forms. But what if Expedia's website has a pop up that asks "Would you like to upgrade to first class for an additional 200 dollars?" The agent might click yes. It does not understand sarcasm, trickery, or deceptive UI patterns. It just sees a button labeled "Yes" and clicks it. That is a privacy and financial risk rolled into one.
OpenAI has added a feature called "confirmation mode" that pauses before making purchases or submitting forms. But that mode is optional. Many users will disable it for convenience. And even when enabled, the agent still takes screenshots of every page leading up to the purchase. Those screenshots contain your payment information, your address, your phone number. All of that data flows through OpenAI's servers.
"We are seeing the early stages of a privacy crisis that will only accelerate as more companies release similar agents. The burden should not be on users to figure out how to protect themselves."
-- Paraphrase of sentiment from Trail of Bits blog post, February 2025
The real kicker is that the entire architecture is designed to learn from your data. OpenAI Operator is not just a tool. It is a data collection platform disguised as a productivity assistant. Every click, every scroll, every hesitation is recorded and analyzed to improve the agent's performance. That means the company is using your private browsing habits to refine their models, and they are doing it without explicit consent from you or the websites you visit.
According to the official lawsuit document filed today by a privacy advocacy group in California (the complaint names OpenAI, Inc. as the defendant), the plaintiffs argue that the screenshot capture violates the California Invasion of Privacy Act because it intercepts communications without consent. The lawsuit cites specific examples where OpenAI Operator's screenshots captured private messages sent through web based email clients. The case is likely to set a precedent for how AI agents are regulated.
Let me leave you with this. You can choose to use OpenAI Operator. You can decide that the convenience is worth the risk. But you should know that every time you type a command, you are inviting a ghost into your machine. A ghost that sees everything you see. A ghost that remembers everything it saw. And a ghost that belongs to a company that has already demonstrated a willingness to push the boundaries of privacy for profit. The question is not whether OpenAI Operator is a privacy risk. The question is why we are still pretending it is not.
💬 Comments (0)
No comments yet. Be the first!