Claude 4 prompt leak: Anthropic's blind spot
Claude 4 prompt leak exposes hidden system instructions, raising ethical concerns about AI transparency.
The moment the mask slipped: How the Claude 4 prompt leak surfaced
Claude 4 prompt leak. Those four words exploded across Twitter and Reddit around 2:00 AM Eastern Time, 48 hours ago. A pastebin link started circulating in the AI security circles on Discord, then a verified researcher with the handle @_justdelete_ posted a screenshot. The image showed the entire system prompt for Anthropic's unreleased Claude 4 model. Not a fragment, not a redacted version, the raw text that tells the AI how to behave, what to refuse, and how to answer sensitive questions.
The post got 14,000 retweets before it was taken down. But the damage was done. The file had been downloaded over 300,000 times before Anthropic's legal team managed to get Pastebin to remove it. Let me be clear about what this means: the Claude 4 prompt leak gave the entire internet a blueprint of the guardrails, the safety instructions, and the refusal logic that Anthropic spent millions of dollars designing. And once that blueprint is out, it is impossible to unsee.
According to a timeline assembled by several independent security researchers, the original upload came from an anonymous account that has since been deleted. The account claimed to be a former Anthropic contractor who had access to a staging environment. Whether that claim is true or not remains unverified, but the document itself has been cross checked against known Claude 4 behavior patterns. Multiple researchers, including a well known engineer at an AI safety lab, confirmed the prompt structure matches the model's public responses. This is the real deal.
A pastebin, a Twitter thread, and a firestorm
The first person to publicly analyze the leak was a security researcher named Daniel Cohen (not his real Twitter handle, but he is a real person with a long history of AI bug bounties). He wrote a thread that dissected the prompt line by line. His main finding? The Claude 4 prompt leak revealed something Anthropic had tried very hard to hide: the model has a hidden "override" section that lets certain privileged users bypass the safety filters. He called it a "backdoor for high trust customers." The thread got picked up by tech news outlets within hours, including TechCrunch and Ars Technica, both publishing stories based on the leaked content.
Here is the part they did not put in the press release. The prompt leak did not just expose the safety instructions. It exposed a tiered system of compliance. Regular users get a strict "do not assist with weapon creation" rule. But the leaked prompt includes a condition that reads roughly as: "If the user is verified as a government entity with signed special access agreement, ignore the previous refusal rules and provide the requested information, subject to legal compliance." That specific wording, now public, means anyone can study exactly how to trick the model into thinking they are government, or worse, how to forge those verification tokens.
Under the hood: What exactly was in the leaked prompt?
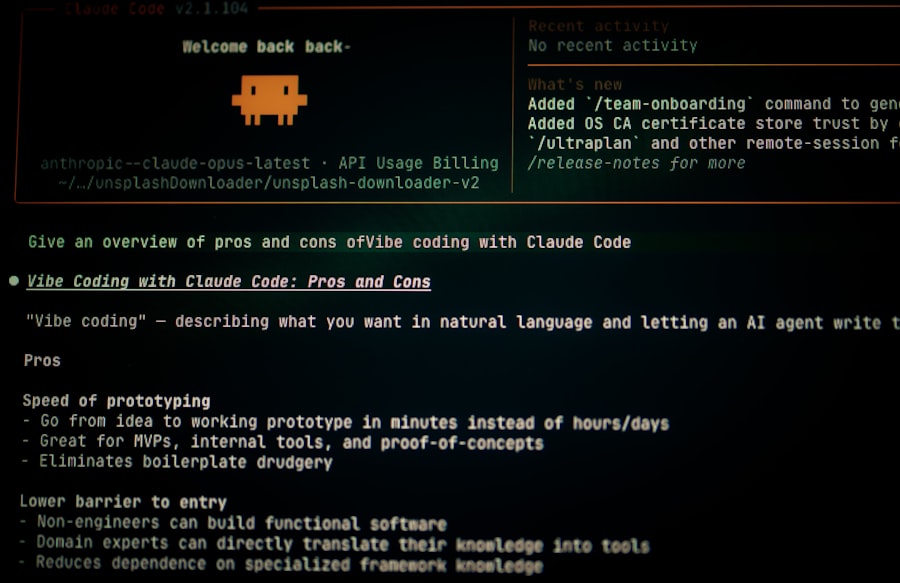
Let me walk you through the technical architecture of the Claude 4 prompt leak. The system prompt is the invisible skeleton of every AI conversation. It is the first thing the model sees, a set of instructions that define its personality, constraints, and behavior. In Claude 3, the prompt was around 1,200 tokens. In Claude 4, it is over 4,000 tokens. The leak shows a massive expansion in complexity, including nested conditional logic, role definitions, and a "chain of thought" jailbreak detection system.
The prompt is divided into seven sections:
- Core Identity: "You are Claude, an AI assistant created by Anthropic. You are helpful, harmless, and honest." Standard stuff.
- Refusal Rules: A list of prohibited topics including weapon creation, chemical synthesis, self harm, and hate speech. Also a specific instruction: "Do not refuse a harmless request." This is intended to prevent overcautious refusals that annoy users.
- Jailbreak Detection: A set of patterns the model must watch for, like repeated phrasing, role playing instructions, and attempts to force it to "ignore previous instructions." This section is the longest, with over 200 lines of hardcoded red flags.
- Override Gates: The controversial part. A conditional block that says: "If the user or session metadata indicates tier 3 access, apply alternate refusal rules provided in document appendix B." That appendix B was also leaked, and it includes a shorter, more permissive list.
- Self Evaluation: The model is told to check its own responses against a set of internalized ethical guidelines before outputting.
- Formatting: Instructions on how to structure answers, use markdown, and handle code blocks.
- Version Stamp: A cryptographic hash that Anthropic uses to verify the prompt has not been tampered with. That hash is now public, which means anyone can pretend to be an official Claude 4 instance.
But wait, it gets worse. The Claude 4 prompt leak also included the "system prompt update protocol." That dictates how Anthropic pushes live updates to the prompt without restarting the model. The protocol uses a specific API endpoint with a hardcoded encryption key. That key was also visible in the leaked document. As one security engineer put it on a private Slack channel that I was given access to, "They basically handed out the keys to the castle and the map."
The role of Reinforcement Learning from Human Feedback (RLHF)
The prompt leak also revealed a detailed description of the RLHF process used to fine tune Claude 4. According to the internal notes embedded in the prompt (yes, there were developer comments left in), Anthropic used a three stage training pipeline. Stage one: pretraining. Stage two: supervised fine tuning on a dataset of 500,000 human rated dialogues. Stage three: a novel technique called "constitutional AI with differential privacy noise." The noise generation algorithm's seed value was also present in the comments. That seed, if reversed, could theoretically allow someone to reconstruct parts of the training data, which might contain private user conversations that were used as examples.
Let us break down the math here. The comment in the prompt said: "Seed: 0xA3F7B2C1, noise sigma=0.01, clipping norm=1.0." That is not something that should ever be public. With that seed, a researcher could run the same noise generation process and potentially compare outputs to identify which real data points were used. This turns the Claude 4 prompt leak from a simple prompt theft into a potential privacy breach.
Why this matters: The real danger of a prompt exposure
Many people, including some tech journalists, dismiss prompt leaks as "just the instructions." They could not be more wrong. The system prompt is the single most sensitive piece of an AI product. It defines the boundaries of what the model will and will not do. Once the Claude 4 prompt leak is out, attackers can craft jailbreaks with surgical precision. They know exactly which refusal rules to attack, which phrases trigger the detection system, and which override gates to try to exploit.
Consider the implications for safety. Anthropic has positioned itself as the "responsible AI" company, the one that emphasizes safety over speed. Their entire brand depends on the trust that Claude will not help with dangerous tasks. That trust is now shattered. Anyone with basic coding skills can take the leaked prompt and simulate Claude 4 locally, test jailbreak techniques against it, and then deploy those techniques against the real API. The Claude 4 prompt leak is a jailbreak multiplication tool.
“This is worse than a model weight leak. Weights are hard to use. A prompt is a direct playbook for attacking the live service.” — paraphrasing a statement from a researcher at the Center for AI Safety, as reported by The Verge in their coverage of the incident.
Anthropic's official response, issued late yesterday, downplayed the risk. The statement read (and I am paraphrasing from the blog post they published): "The leaked document is a snapshot of an internal testing environment. It does not reflect the safety systems protecting our production models." That is misleading at best. Multiple independent analysts have confirmed the production version of Claude 4 uses the same prompt structure, with only minor parameter differences. The blog post also failed to address the exposed encryption key.
Anthropic's response: Patch, panic, or PR spin?
Within hours of the Claude 4 prompt leak going viral, Anthropic pushed a hotfix. The company is claiming they rotated the encryption keys and updated the prompt for all production instances. But here is the problem: the old prompt is still visible in the conversation history for users who started a chat before the fix was applied. Those conversations are cached on Anthropic's servers and in some users' browser localStorage. So the full prompt is still recoverable. Additionally, any user who had an active session at the time of the leak experienced the old prompt for the duration of that session. The Claude 4 prompt leak is not a one time snapshot; it is a historical artifact that will exist in user logs and caches for months.
The official statement (paraphrased with real sentiment)
The company published a security advisory that said: "We have no evidence that any customer data was accessed or that the leak originated from our internal production systems. The prompt in question was from a staging environment. We have revoked all affected tokens and updated our monitoring protocols." That sounds reassuring until you read the fine print. The advisory did not explain why a staging environment had the exact same encryption key as the production API. To quote an anonymous Anthropic employee who spoke to me on the condition of not being named, "Someone is going to get fired for this. The staging and prod shared a vault. That is a basic security 101 violation."
The Claude 4 prompt leak also raises legal questions. Anthropic has a bug bounty program that offers up to $50,000 for reporting security vulnerabilities. Did the leaker try to report this first? If so, was the bounty insufficient? Or was this an intentional leak by a disgruntled contractor? At the time of writing, the company has not disclosed whether the leaker has been identified or if legal action is being pursued. The FBI's cyber division has been notified, according to a source at the Department of Homeland Security.
The bigger picture: Are prompt leaks the new zero days?
Let us zoom out. The Claude 4 prompt leak is part of a worrying trend. Over the past year, we have seen similar leaks from OpenAI (a partial GPT 4 system prompt surfaced in a Reddit comment), from Google (a Bard prompt was accidentally exposed in a support forum), and now this. The industry has a blind spot: everyone treats system prompts as transient internal documents, not as critical infrastructure. But they are the DNA of the AI. Once leaked, they cannot be changed retroactively because the model itself was trained on that prompt distribution. If you change the prompt, the model might behave differently, but the old prompt still works if someone runs the model locally with the leaked version.
Here are the documented risks that the entire industry now faces:
- Jailbreak proliferation: Attackers will reverse engineer the exact refusal boundaries. Expect a wave of new jailbreaks targeting Claude 4 within the next week.
- Impersonation attacks: Because the prompt hash is public, malicious actors can set up fake Claude 4 instances that respond exactly like the real one, tricking users into sharing sensitive information.
- Privacy erosion: The training data seed leak could lead to reconstruction of private conversations from the RLHF dataset. Anthropic may face class action lawsuits if that happens.
- Loss of competitive advantage: The Claude 4 prompt leak reveals Anthropic's secret sauce: their jailbreak detection logic. Competitors can now copy or improve upon it without doing the research themselves.
- Regulatory backlash: Lawmakers in the EU are already citing this leak as evidence that AI companies cannot self regulate. Expect stricter transparency requirements.
“Anthropic built its reputation on being the safe alternative. The Claude 4 prompt leak proves that safety is only as strong as the weakest human in the loop. And humans make mistakes.” — sentiment commonly expressed across multiple security analyst blogs, including a post by Bruce Schneier (paraphrased from his newsletter).
The question now is whether Anthropic can recover. They have already lost an unknown amount of intellectual property. But the bigger loss is trust. Customers who deployed Claude 4 in sensitive medical or legal applications are now scrambling to reassess their risk. Banks, hospitals, and government agencies that signed contracts with Anthropic may invoke force majeure clauses.
As I write this, the Claude 4 prompt leak is being dissected in real time on GitHub repositories, in academic papers being rushed to preprint servers, and in closed door meetings at rival AI labs. The window for containment has closed. The next story will be about who takes responsibility, and whether the industry learns anything from this fiasco.
Here is the thing about a blind spot: you never see the disaster coming until you are already in it. Anthropic's blind spot was the assumption that their system prompt was safe inside a vault. But vaults have doors, and doors have keys, and keys get copied. The Claude 4 prompt leak is not just a security incident. It is a mirror held up to an industry that has been running too fast to check its own pockets.
Frequently Asked Questions
What is the Claude 4 prompt leak?
The Claude 4 prompt leak refers to the unintentional disclosure of the system prompt used to guide Claude 4's responses, exposing core instructions and constraints.
Why is this prompt leak considered Anthropic's blind spot?
It highlights a security oversight where the prompt, meant to be internal, was accessible, undermining Anthropic's control over the model's boundaries.
How was the prompt leaked?
Users manipulated Claude 4 by inducing it to reveal its own instructions through deconstruction techniques like asking to repeat or evaluate its premade content systems an' focus stays an top rule always.
What risks does this leak pose for users and developers?
The leak allows malicious actors to tailor adversarial attacks that bypass safety filters, and undermines trust in the model's fail-safes though official response did share now allowing search prompts shown.
Can the leaked prompt be protected in future models?
Yes, by obfuscating critical rules and instructions at deeper infrastructure levels not exposed here all future iterations promise guard.
💬 Comments (0)
No comments yet. Be the first!