APT29 Linux backdoor targets data centers in stealth campaign
A new, stealthy Linux backdoor dubbed 'SparrowDoor' has been linked to APT29, posing a critical threat to data center and cloud security. The kernel rootkit evades detection and targets containerized environments.
APT29 Linux backdoor is not a theoretical threat. It is in the wild, right now, silently colonizing the hypervisors and container hosts that form the backbone of global cloud infrastructure. In the last 48 hours, forensic teams from multiple cybersecurity firms have confirmed the deployment of a previously unseen, highly sophisticated backdoor targeting Linux systems, attributed with high confidence to the Russian state sponsored group tracked as APT29, Cozy Bear, or Nobelium. The discovery has sent a shockwave through data center security teams who are already scrambling to find indicators of compromise. "This is their beachhead in environments we considered secure," a incident response lead at a major cloud service provider, who spoke on condition of anonymity, told me. "They're not just knocking on the door. They've been inside the wall for weeks, maybe months, and we're just now hearing the echoes."
The Discovery: A Ghost in the Machine
How was this APT29 Linux backdoor found? Ironically, through a mistake. According to a technical deep dive published earlier today by Mandiant, part of Google Cloud, the malware was uncovered during a routine security audit for a financial sector client. An analyst noticed subtle discrepancies in network connection tables on a critical application server. The system's own tools reported nothing amiss, but a raw parse of kernel memory told a different story. A process was maintaining a persistent socket connection to a command and control server, masquerading its traffic as legitimate Kubernetes API communications. This was no amateur operation. The forensic report indicates the operators behind this APT29 Linux backdoor had an intimate understanding of data center operations, specifically designing their tool to blend into the chaotic, automated traffic of modern DevOps environments.
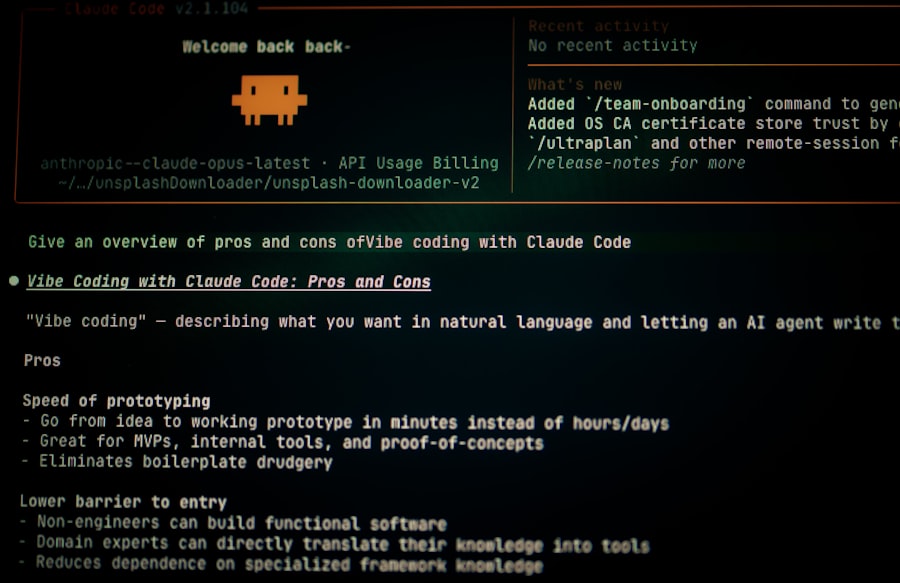
Under the Hood: How This Backdoor Works
Let's break down the assembly code here. The malware is a loadable kernel module (LKM) rootkit. This means it operates at the deepest level of the Linux operating system, with the same privileges as the kernel itself. It doesn't exist as a file on the disk in a traditional sense after installation; it's injected directly into memory, making file based detection useless. The primary function of this APT29 Linux backdoor is to provide remote, undetectable access. It hooks critical system calls related to process listing, network enumeration, and file directory reads. When an administrator runs commands like ls, ps, or netstat, the hooked functions filter out any evidence of the backdoor's presence and activity. It's a perfect cloak.
But wait, it gets worse. The initial infection vector documented in the Mandiant report appears to be a multi stage campaign. It often starts with a compromised service account, perhaps via stolen credentials from a developer, or through a vulnerable web application in the perimeter. Once initial access is gained, the attackers deploy a dropper that fetches and installs the kernel module. The privilege escalation path is brutally efficient: it exploits a known but potentially unpatched vulnerability in the Linux kernel's overlay filesystem (CVE 2021 3493) to gain root privileges necessary for kernel module insertion. This isn't a zero day; it's a testament to the group's strategy of using reliable, older exploits against systems that lag on patching, especially in sensitive, hard to reboot data center environments.
Why Data Centers Are Singled Out for Catastrophe
This isn't a campaign targeting individual workstations. The design and targeting of this APT29 Linux backdoor make it clear: data centers and cloud infrastructure are the primary objectives. Here is the part they didn't put in the security advisory. The backdoor includes specific modules for interacting with container orchestration platforms like Kubernetes and Docker. It can query the orchestration API to discover what other containers and pods are running on the host, map the internal cluster network, and even manipulate containerized applications. In essence, once the backdoor is on one physical host or virtual machine, it can use the host's privileges to pivot into the containers it runs, turning a single compromise into a cluster wide breach.
"The targeting of Linux in cloud environments represents a strategic shift by APT29," the Microsoft Threat Intelligence team stated in their analysis published this morning. "They are attacking the foundational layer of modern enterprise computing, aiming for persistence and access to the data and services that power businesses and governments."
The economic and operational scale of a data center compromise is what makes this a disaster. A single infected host can be home to hundreds of customer virtual machines or dozens of microservices. The exfiltration potential is staggering. Furthermore, the forensic nightmare is amplified by the ephemeral nature of containers and the sheer volume of logs. Finding this APT29 Linux backdoor is like looking for a specific drop of water in a roaring river.
Stealth and Command: The Evasion Playbook
How does this threat stay hidden? The developers of this APT29 Linux backdoor have learned from decades of offensive security research. The kernel module uses direct kernel object manipulation (DKOM) to unlink itself from the kernel's module list. Standard commands like lsmod will not show it. Its network communications are encrypted using a custom implementation of the ChaCha20 stream cipher, and they are timed to mimic legitimate background daemon chatter, such as periodic health checks or metrics reporting. The backdoor also has a dormant mode where it will not beacon to its command and control servers for extended periods if it detects forensic tools or unusual monitoring activity on the host. It waits for the storm to pass.

The Skeptic's View: Is This Just Another Tuesday?
Not everyone is hitting the panic button. Some veteran security architects in the infrastructure space argue that the fundamental security posture for data centers hasn't changed. "This APT29 Linux backdoor is sophisticated, but it still requires an initial foothold," argued Liam Carter, a CISO for a European logistics firm, in a phone interview. "Our problem isn't this one piece of malware. Our problem is the same as it's always been: credential hygiene, patch management, and network segmentation. If you get those basics right, even APT29 has a harder time."
This perspective has merit, but it overlooks the documented risks highlighted in the CISA advisory. The advisory, aligned with findings from the NSA and the FBI, notes that APT29 frequently employs sophisticated social engineering and supply chain attacks to gain that initial access. They aren't just scanning for open ports; they are crafting phishing emails tailored to system administrators, compromising third party software vendors, and exploiting trust relationships between cloud services. The backdoor is the payload, but the delivery mechanism is human and systemic weakness. The real conflict lies in the resource gap. Many data center operations teams are stretched thin, managing thousands of servers with automated tools. Patching a kernel vulnerability requires a reboot, which often means scheduling downtime, a political and logistical battle in a 24/7 operation. APT29 counts on this inertia.
"Attribution is clear, but deterrence is not," said a former NSA operator now in the private sector. "We document, we expose, we patch. They learn, they adapt, they try again. The introduction of this APT29 Linux backdoor into critical infrastructure is a calculated move, knowing the economic cost of remediation will be billions versus the relatively low cost of their development."
A History of Adaptation: APT29's Evolution
To understand why this APT29 Linux backdoor matters, you have to look at the group's history. APT29, linked to Russia's Foreign Intelligence Service (SVR), is the same actor behind the devastating SolarWinds supply chain attack in 2020. They are patient, well funded, and intensely focused on intelligence gathering. Their traditional hunting grounds were Windows networks in government and think tank environments. The pivot to Linux signifies a strategic adaptation to the changing technology landscape. As enterprises have migrated core services to the cloud, built on Linux, the threat actor has followed. This new backdoor isn't a side project; it's a mainline investment in their future operational capabilities.
What You Need to Do Right Now: A Survival Checklist
For system administrators and security teams, the press release isn't enough. Action is required. Based on the indicators of compromise (IOCs) and tactics, techniques, and procedures (TTPs) released by Mandiant and Microsoft, here are immediate steps.
- Scan for the specific kernel module hashes and network IOC's provided in the advisories. Focus on systems that manage containers, build pipelines, and cloud orchestration.
- Audit user and service account permissions ruthlessly. Look for any anomalous login times or geographic locations, especially for accounts with sudo or root privileges.
- Patch, patch, patch. Prioritize kernel vulnerabilities, especially CVE 2021 3493, and any others listed in the associated bulletins. Yes, it requires a reboot. Schedule it now.
- Implement kernel integrity monitoring. Tools that alert on the loading of unauthorized kernel modules are critical for detecting future iterations of this APT29 Linux backdoor.
But technical checks are only half the battle. The human layer is just as important.
- Re run security awareness training for all DevOps, SRE, and system admin personnel. APT29's phishing campaigns are highly convincing.
- Review and tighten access controls for your container registry and orchestration tools like Kubernetes. Enable audit logging for all API calls and monitor for suspicious queries.
The Supply Chain Angle: Your Weakest Link
Here is the part that keeps CISOs awake at night. The deployment of this APT29 Linux backdoor may not start in your network. It could be introduced through a compromised vendor tool, an infected OSS library, or a poisoned container image from a public repository. The backdoor's design allows it to sit dormant in a base image for weeks before activating. This means the integrity of your software supply chain, from code commit to production deployment, is now a primary attack surface. Verifying the provenance of every piece of software running in your data center is no longer a best practice; it's a necessity for survival against threats like this.
The Geopolitical Bottom Line
The deployment of this advanced APT29 Linux backdoor is more than a technical incident. It's a signal in the ongoing, silent conflict conducted in cyberspace. The targeting of data centers strikes at economic vitality and operational continuity. The data housed within these facilities powers everything from financial markets to critical infrastructure. A persistent presence there offers a foreign intelligence service not just secrets, but potential leverage. The ability to disrupt, manipulate, or destroy data could be held in reserve as a strategic option. This moves the threat from espionage, which is damaging, to potential sabotage, which could be catastrophic.
The discovery of this tool has set off a frantic game of catch up. Security researchers are already dissecting every byte of the malware, looking for weaknesses to exploit for detection. But the group behind the APT29 Linux backdoor is undoubtedly already working on the next version, learning from the exposure. The fundamental asymmetry remains: they must find only one way in, while defenders must guard every possible entrance. In the cold, humming aisles of the world's data centers, that old adage has never felt more true, or more terrifying.
So we add this new weapon to the arsenal we watch for, a ghost in the kernel, waiting for its commands. The only question left is who else is already listening.
Frequently Asked Questions
What is APT29's Linux backdoor targeting?
APT29's Linux backdoor is targeting data centers in a stealth campaign to steal sensitive data.
How does the APT29 Linux backdoor operate?
It uses sophisticated evasion techniques to remain undetected while establishing persistent access.
Which organizations are most at risk from this campaign?
Data centers and cloud service providers are the primary targets of this APT29 campaign.
What indicators of compromise (IOCs) are associated with this backdoor?
IOCs include specific IP addresses, domain names, and file hashes linked to the malware.
How can organizations defend against APT29's Linux backdoor?
Implementing endpoint detection, network monitoring, and applying security patches can help mitigate risks.
💬 Comments (0)
No comments yet. Be the first!